SearchSploit – The Manual
Included in our Exploit Database repository on GitLab is searchsploit, a command line search tool for Exploit-DB that also allows you to take a copy of Exploit Database with you, everywhere you go. SearchSploit gives you the power to perform detailed off-line searches through your locally checked-out copy of the repository. This capability is particularly useful for security assessments on segregated or air-gapped networks without Internet access.
Many exploits contain links to binary files that are not included in the standard repository but can be found in our Exploit Database Binary Exploits repository instead. If you anticipate you will be without Internet access on an assessment, ensure you check out both repositories for the most complete set of data.
This guide is for version 4 of SearchSploit. Note, The name of this utility is SearchSploit and as its name indicates, it will search for all exploits and shellcode. It will not include any results for Google Hacking Database, but it can include Papers if configured (correctly!).
How to Install SearchSploit
Kali Linux
If you are using the standard GNOME build of Kali Linux, the exploitdb package is already included by default! However, if you are using the Kali Light variant or your own custom-built ISO, you can install the package manually as follows:
kali@kali:~$ sudo apt update && sudo apt -y install exploitdbYou may wish to install some other related packages: exploitdb-papers and exploitdb-bin-sploits.
Linux
If you are not using Kali Linux, the exploitdb package may not be available through the package manager in which case, you can continue by following the instructions under the 'Git' tab.
If you have Homebrew installed, running the following will get you set up:
user@MacBook:~$ brew update && brew install exploitdbAlternatively, if you do not have brew installed, you can continue by following the instructions under the 'Git' tab.
At this time, there is no easy or straightforward way to use SearchSploit on Windows. The best alternative we can suggest would be to use Kali Linux in a virtual machine, docker, or Windows Subsystem for Linux.
On *nix systems, all you really need is either “CoreUtils” or “utilities” (e.g.
bash, sed, grep, awk, etc.), as well as git. These are installed
by default on many different Linux distributions, including OS X/macOS.
You can easily check out the git repository by running the following:
$ git clone https://gitlab.com/exploit-database/exploitdb.git /opt/exploit-database
An optional step that will make using SearchSploit easier is to include it into
your $PATH.
Example: In the following output, the directory
/usr/local/bin is included in the $PATH
environment variable:
$ echo $PATH
/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin
$With this in mind, you can then create a symbolic link in the /usr/local/bin directory that points to searchsploit, allowing you to run it without providing the full path:
$ ln -sf /opt/exploit-database/searchsploit /usr/local/bin/searchsploit
$The last stage is to copy the resource file and edit it to match your system environment so it points to the correct directories:
$ cp -n /opt/exploit-database/.searchsploit_rc ~/
$
$ vim ~/.searchsploit_rcEach section in the resource file (.searchsploit_rc) is split into sections (such as Exploits, Shellcodes, Papers).
- files_array – A Comma-Separated Value file (files_*.CSV) that contains all the data that relates to that section (such as: EDB-ID, Title, Author, Date Published, etc)
- path_array – This points to the directory where all the files are located. **This is often the only value that needs altering**
- name_array – The value name to display in SearchSploit for that section
- git_array – The remote git location to use to update the local copy
- package_array – The package name to use when there is a package manager available (such as apt or brew)
If you want to include Exploit-DB Papers, you can check out the git repository. Afterwards, edit searchsploit’s resource file so paper’s path_array points to the same directory you just checked out.
Updating SearchSploit
If you are using Kali Linux, you can expect the exploitdb package to be
updated weekly. If you are
using Homebrew or Git, you can expect
daily updates (at 05:05 UTC).
Regardless of how you installed SearchSploit, all you need to do in order to update it is
run the following:
$ searchsploit -uIf you are using the Kali Linux package and haven’t updated since before 20 September 2016 (shame on you), you will first need to update the package in the traditional manner:
kali@kali:~$ sudo apt update && sudo apt -y full-upgradePlease note, we do not recommend you use GitLab’s .zip or the legacy archive.tar.bz2 packages to update.
Using SearchSploit
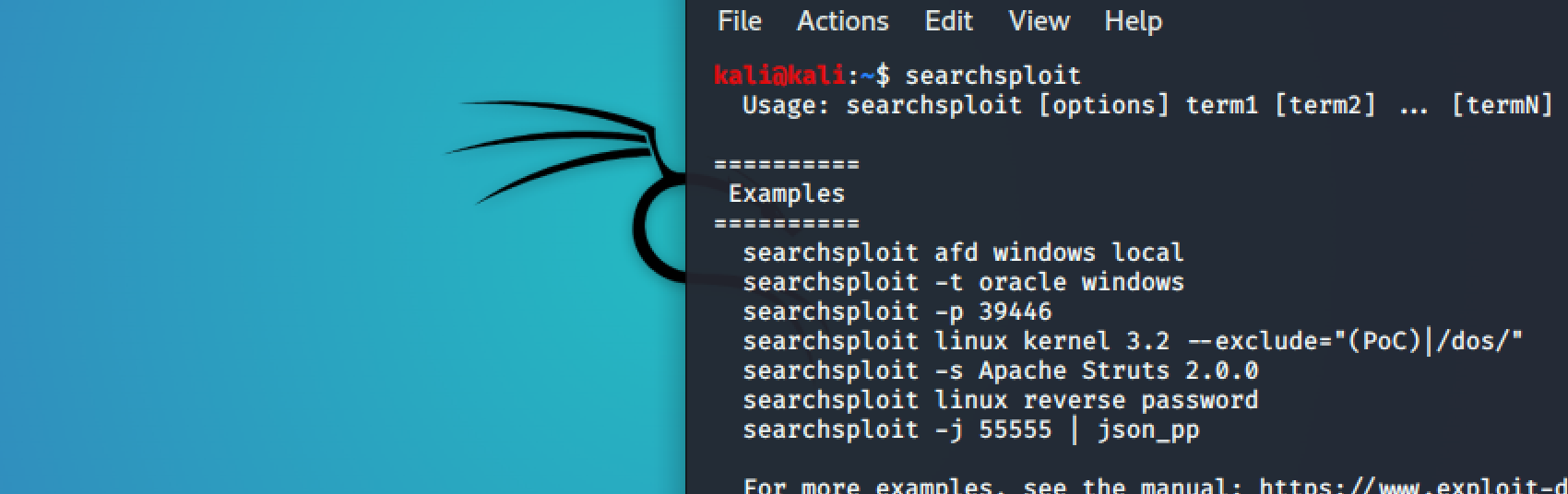
Help Screen
By using -h, you can see all the features and options that are available to
you:
kali@kali:~$ searchsploit -h
Usage: searchsploit [options] term1 [term2] ... [termN]
==========
Examples
==========
searchsploit afd windows local
searchsploit -t oracle windows
searchsploit -p 39446
searchsploit linux kernel 3.2 --exclude="(PoC)|/dos/"
searchsploit -s Apache Struts 2.0.0
searchsploit linux reverse password
searchsploit -j 55555 | jq
searchsploit --cve 2021-44228
For more examples, see the manual: https://www.exploit-db.com/searchsploit
=========
Options
=========
## Search Terms
-c, --case [term] Perform a case-sensitive search (Default is inSEnsITiVe)
-e, --exact [term] Perform an EXACT & order match on exploit title (Default is an AND match on each term) [Implies "-t"]
e.g. "WordPress 4.1" would not be detect "WordPress Core 4.1")
-s, --strict Perform a strict search, so input values must exist, disabling fuzzy search for version range
e.g. "1.1" would not be detected in "1.0 < 1.3")
-t, --title [term] Search JUST the exploit title (Default is title AND the file's path)
--exclude="term" Remove values from results. By using "|" to separate, you can chain multiple values
e.g. --exclude="term1|term2|term3"
--cve [CVE] Search for Common Vulnerabilities and Exposures (CVE) value
## Output
-j, --json [term] Show result in JSON format
-o, --overflow [term] Exploit titles are allowed to overflow their columns
-p, --path [EDB-ID] Show the full path to an exploit (and also copies the path to the clipboard if possible)
-v, --verbose Display more information in output
-w, --www [term] Show URLs to Exploit-DB.com rather than the local path
--id Display the EDB-ID value rather than local path
--disable-colour Disable colour highlighting in search results
## Non-Searching
-m, --mirror [EDB-ID] Mirror (aka copies) an exploit to the current working directory
-x, --examine [EDB-ID] Examine (aka opens) the exploit using $PAGER
## Non-Searching
-h, --help Show this help screen
-u, --update Check for and install any exploitdb package updates (brew, deb & git)
## Automation
--nmap [file.xml] Checks all results in Nmap's XML output with service version
e.g.: nmap [host] -sV -oX file.xml
=======
Notes
=======
* You can use any number of search terms
* By default, search terms are not case-sensitive, ordering is irrelevant, and will search between version ranges
* Use '-c' if you wish to reduce results by case-sensitive searching
* And/Or '-e' if you wish to filter results by using an exact match
* And/Or '-s' if you wish to look for an exact version match
* Use '-t' to exclude the file's path to filter the search results
* Remove false positives (especially when searching using numbers - i.e. versions)
* When using '--nmap', adding '-v' (verbose), it will search for even more combinations
* When updating or displaying help, search terms will be ignored
kali@kali:~$Basic Search
Simply add any number of search terms you wish to look for:
kali@kali:~$ searchsploit afd windows local
--------------------------------------------------------------------------------------- ---------------------------------
Exploit Title | Path
--------------------------------------------------------------------------------------- ---------------------------------
Microsoft Windows (x86) - 'afd.sys' Local Privilege Escalation (MS11-046) | windows_x86/local/40564.c
Microsoft Windows - 'afd.sys' Local Kernel (PoC) (MS11-046) | windows/dos/18755.c
Microsoft Windows - 'AfdJoinLeaf' Local Privilege Escalation (MS11-080) (Metasploit) | windows/local/21844.rb
Microsoft Windows 7 (x64) - 'afd.sys' Dangling Pointer Privilege Escalation (MS14-040) | windows_x86-64/local/39525.py
Microsoft Windows 7 (x86) - 'afd.sys' Dangling Pointer Privilege Escalation (MS14-040) | windows_x86/local/39446.py
Microsoft Windows XP - 'afd.sys' Local Kernel Denial of Service | windows/dos/17133.c
Microsoft Windows XP/2003 - 'afd.sys' Local Privilege Escalation (K-plugin) (MS08-066) | windows/local/6757.txt
Microsoft Windows XP/2003 - 'afd.sys' Local Privilege Escalation (MS11-080) | windows/local/18176.py
--------------------------------------------------------------------------------------- ---------------------------------
Shellcodes: No Result
kali@kali:~$
Note, SearchSploit uses an AND operator, not an
OR operator. The more terms that are used, the more results will be
filtered out.
Pro Tip: Do not use abbreviations (use SQL Injection, not SQLi).
Pro Tip: If you are not receiving the expected results, try searching more
broadly by using more general terms (use Kernel 2.6 or Kernel 2.x, not Kernel 2.6.25).
Title Searching
By default, searchsploit will check BOTH the title of the exploit as well as the path.
Depending on the search criteria, this may bring up false positives (especially when
searching for terms that match platforms and version numbers). Searches can be restricted
to the titles by using the -t option:
kali@kali:~$ searchsploit -t oracle windows
--------------------------------------------------------------------------------------- ---------------------------------
Exploit Title | Path
--------------------------------------------------------------------------------------- ---------------------------------
Oracle 10g (Windows x86) - 'PROCESS_DUP_HANDLE' Local Privilege Escalation | windows_x86/local/3451.c
Oracle 9i XDB (Windows x86) - FTP PASS Overflow (Metasploit) | windows_x86/remote/16731.rb
Oracle 9i XDB (Windows x86) - FTP UNLOCK Overflow (Metasploit) | windows_x86/remote/16714.rb
Oracle 9i XDB (Windows x86) - HTTP PASS Overflow (Metasploit) | windows_x86/remote/16809.rb
Oracle MySQL (Windows) - FILE Privilege Abuse (Metasploit) | windows/remote/35777.rb
Oracle MySQL (Windows) - MOF Execution (Metasploit) | windows/remote/23179.rb
Oracle MySQL for Microsoft Windows - Payload Execution (Metasploit) | windows/remote/16957.rb
Oracle VirtualBox Guest Additions 5.1.18 - Unprivileged Windows User-Mode Guest Code Do| multiple/dos/41932.cpp
Oracle VM VirtualBox 5.0.32 r112930 (x64) - Windows Process COM Injection Privilege Esc| windows_x86-64/local/41908.txt
--------------------------------------------------------------------------------------- ---------------------------------
Shellcodes: No Result
kali@kali:~$
kali@kali:~$ searchsploit oracle windows | wc -l
100
kali@kali:~$
If we did not use -t, we would have 94 (6 lines are in the heading/footer)
results, rather than 9.
Removing Unwanted Results
We can remove unwanted results by using the --exclude option. We are also able
to remove multiple terms by separating the value with a | (pipe). This can be
demonstrated by the following:
kali@kali:~$ searchsploit linux kernel 3.2 --exclude="(PoC)|/dos/"
--------------------------------------------------------------------------------------- ---------------------------------
Exploit Title | Path
--------------------------------------------------------------------------------------- ---------------------------------
Linux Kernel (Solaris 10 / < 5.10 138888-01) - Local Privilege Escalation | solaris/local/15962.c
Linux Kernel 2.6.22 < 3.9 (x86/x64) - 'Dirty COW /proc/self/mem' Race Condition Privile| linux/local/40616.c
Linux Kernel 2.6.22 < 3.9 - 'Dirty COW /proc/self/mem' Race Condition Privilege Escalat| linux/local/40847.cpp
Linux Kernel 2.6.22 < 3.9 - 'Dirty COW PTRACE_POKEDATA' Race Condition (Write Access Me| linux/local/40838.c
Linux Kernel 2.6.22 < 3.9 - 'Dirty COW' 'PTRACE_POKEDATA' Race Condition Privilege Esca| linux/local/40839.c
Linux Kernel 2.6.22 < 3.9 - 'Dirty COW' /proc/self/mem Race Condition (Write Access Met| linux/local/40611.c
Linux Kernel 2.6.39 < 3.2.2 (Gentoo / Ubuntu x86/x64) - 'Mempodipper' Local Privilege E| linux/local/18411.c
Linux Kernel 2.6.39 < 3.2.2 (x86/x64) - 'Mempodipper' Local Privilege Escalation (2) | linux/local/35161.c
Linux Kernel 3.0 < 3.3.5 - 'CLONE_NEWUSER|CLONE_FS' Local Privilege Escalation | linux/local/38390.c
Linux Kernel 3.14-rc1 < 3.15-rc4 (x64) - Raw Mode PTY Echo Race Condition Privilege Esc| linux_x86-64/local/33516.c
Linux Kernel 3.2.0-23/3.5.0-23 (Ubuntu 12.04/12.04.1/12.04.2 x64) - 'perf_swevent_init'| linux_x86-64/local/33589.c
Linux Kernel 3.2.x - 'uname()' System Call Local Information Disclosure | linux/local/37937.c
Linux Kernel 3.4 < 3.13.2 (Ubuntu 13.04/13.10 x64) - 'CONFIG_X86_X32=y' Local Privilege| linux_x86-64/local/31347.c
Linux Kernel 3.4 < 3.13.2 (Ubuntu 13.10) - 'CONFIG_X86_X32' Arbitrary Write (2) | linux/local/31346.c
Linux Kernel 4.8.0 UDEV < 232 - Local Privilege Escalation | linux/local/41886.c
Linux Kernel < 3.16.1 - 'Remount FUSE' Local Privilege Escalation | linux/local/34923.c
Linux Kernel < 3.16.39 (Debian 8 x64) - 'inotfiy' Local Privilege Escalation | linux/local/44302.c
Linux Kernel < 3.2.0-23 (Ubuntu 12.04 x64) - 'ptrace/sysret' Local Privilege Escalation| linux_x86-64/local/34134.c
Linux Kernel < 3.4.5 (Android 4.2.2/4.4 ARM) - Local Privilege Escalation | arm/local/31574.c
Linux Kernel < 3.5.0-23 (Ubuntu 12.04.2 x64) - 'SOCK_DIAG' SMEP Bypass Local Privilege | linux/local/44299.c
Linux Kernel < 3.8.9 (x86-64) - 'perf_swevent_init' Local Privilege Escalation (2) | linux_x86-64/local/26131.c
Linux Kernel < 3.8.x - open-time Capability 'file_ns_capable()' Local Privilege Escalat| linux/local/25450.c
Linux kernel < 4.10.15 - Race Condition Privilege Escalation | linux/local/43345.c
Linux Kernel < 4.11.8 - 'mq_notify: double sock_put()' Local Privilege Escalation | linux/local/45553.c
Linux Kernel < 4.13.9 (Ubuntu 16.04 / Fedora 27) - Local Privilege Escalation | linux/local/45010.c
Linux Kernel < 4.15.4 - 'show_floppy' KASLR Address Leak | linux/local/44325.c
Linux Kernel < 4.4.0-116 (Ubuntu 16.04.4) - Local Privilege Escalation | linux/local/44298.c
Linux Kernel < 4.4.0-21 (Ubuntu 16.04 x64) - 'netfilter target_offset' Local Privilege | linux/local/44300.c
Linux Kernel < 4.4.0-83 / < 4.8.0-58 (Ubuntu 14.04/16.04) - Local Privilege Escalation | linux/local/43418.c
Linux Kernel < 4.4.0/ < 4.8.0 (Ubuntu 14.04/16.04 / Linux Mint 17/18 / Zorin) - Local P| linux/local/47169.c
--------------------------------------------------------------------------------------- ---------------------------------
Shellcodes: No Result
kali@kali:~$
kali@kali:~$ searchsploit linux kernel 3.2 | wc -l
47
kali@kali:~$
By doing this, we slim the results down to 30 rather than 41 (6 lines are for the
heading/footer)!
You may of also noticed, "3.2" isn't always visible in the results. That is because
SearchSploit by default, will try to detect the version, and then search between
any ranges in the title. This behaviour can be disabled by doing -s.
Pro Tip: By doing: searchsploit linux kernel
--exclude="(PoC)|/dos/" | grep ' 3.2' (space before the version),
you'll get even "cleaner" output (sorted based on version without any
heading/footers).
Piping Output (Alternative Method of Removing Unwanted Results)
The output from searchsploit can be piped into any other program, which is especially
useful when outputting the results in JSON format (using the -j option). With
this, it is possible to remove any unwanted exploits by using grep. In the following
example, we use grep to filter out any "Denial of Service (DoS)" results.
kali@kali:~$ searchsploit XnView | grep -v '/dos/'
--------------------------------------------------------------------------------------- ---------------------------------
Exploit Title | Path
--------------------------------------------------------------------------------------- ---------------------------------
XnView 1.90.3 - '.xpm' Local Buffer Overflow | windows/local/3777.c
XnView 1.92.1 - 'FontName' Slideshow Buffer Overflow | windows/local/5346.pl
XnView 1.92.1 - Command-Line Arguments Buffer Overflow | windows/remote/31405.c
XnView 1.93.6 - '.taac' Local Buffer Overflow | windows/local/5951.c
XnView 1.97.4 - '.MBM' File Remote Heap Buffer Overflow | windows/remote/34143.txt
--------------------------------------------------------------------------------------- ---------------------------------
kali@kali:~$
kali@kali:~$ searchsploit XnView | wc -l
23
kali@kali:~$
By piping the search results into grep, we managed to filter the results down to 5 rather
than 17 (6 lines are in the heading/footer)!
Pro Tip: We recommend using "/dos/" with grep rather than "dos" so the
filter is applied to the path, rather than the title. Although denial of service entries
may not include "dos" in their title, they will nevertheless have "dos" in the path.
Removing results based on the path will also ensure you don't inadvertently filter out
results that legitimately contain "dos" in their title (i.e.: EDB-ID #24623).
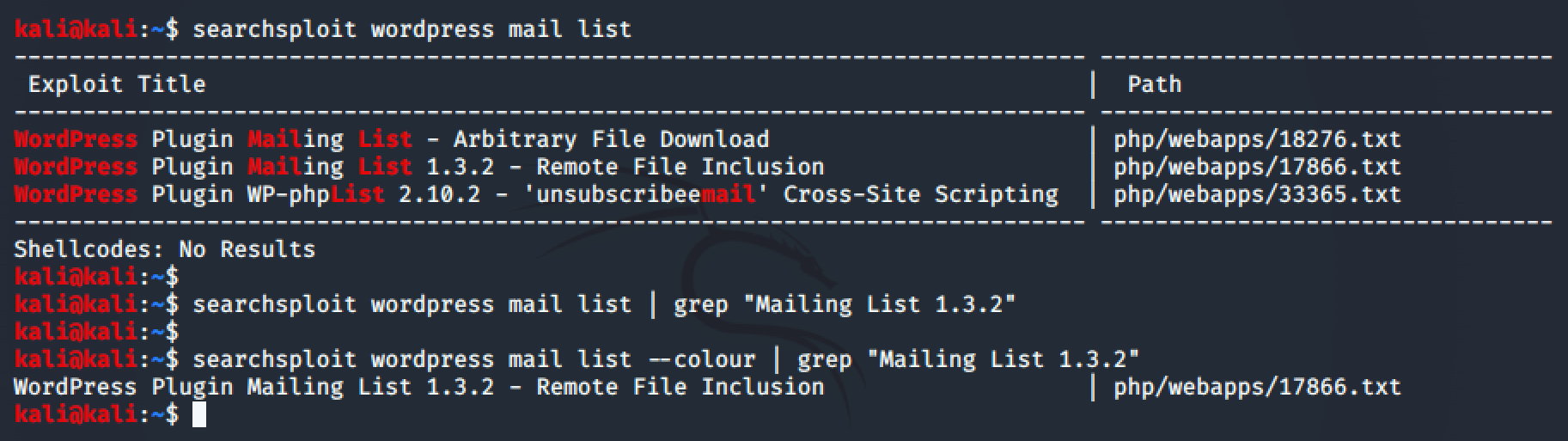
Colour Output
By default, searchsploit highlights the search terms in the results when they are displayed
to the user. This works by inserting invisible characters into the output before and after
the colour changes.
Now, if you were to pipe the output (for example, into grep) and try to match a phrase of
both highlighted and non-highlighted text in the output, it would not be successful. This
can be solved by using the --disable-colour option (--disable-color works as
well).
Copy To Clipboard
So now that we have found the exploit we are looking for, there are various ways to access
it quickly.
By using -p, we are able to get some more information about the exploit, as
well as copy the complete path to the exploit onto the clipboard:
kali@kali:~$ searchsploit 39446
--------------------------------------------------------------------------------------- ---------------------------------
Exploit Title | Path
--------------------------------------------------------------------------------------- ---------------------------------
Microsoft Windows 7 (x86) - 'afd.sys' Dangling Pointer Privilege Escalation (MS14-040) | windows_x86/local/39446.py
--------------------------------------------------------------------------------------- ---------------------------------
Shellcodes: No Result
kali@kali:~$
kali@kali:~$ searchsploit -p 39446
Exploit: Microsoft Windows 7 (x86) - 'afd.sys' Dangling Pointer Privilege Escalation (MS14-040)
URL: https://www.exploit-db.com/exploits/39446
Path: /usr/share/exploitdb/exploits/windows_x86/local/39446.py
Codes: CVE-2014-1767, MS14-040
Verified: False
File Type: Python script text executable, ASCII text
Copied EDB-ID #39446's path to the clipboard
kali@kali:~$
kali@kali:~$ /usr/share/exploitdb/exploits/windows_x86/local/39446.pyCopy To Folder
We recommend that you do not alter the exploits in your local copy of the database.
Instead, make a copy of ones that are of interest and use them from a working directory. By
using the -m option, we are able to select as many exploits we like to be
copied into the same folder that we are currently in:
kali@kali:~$ searchsploit MS14-040
--------------------------------------------------------------------------------------- ---------------------------------
Exploit Title | Path
--------------------------------------------------------------------------------------- ---------------------------------
Microsoft Windows 7 (x64) - 'afd.sys' Dangling Pointer Privilege Escalation (MS14-040) | exploits/windows_x86-64/local/39525.py
Microsoft Windows 7 (x86) - 'afd.sys' Dangling Pointer Privilege Escalation (MS14-040) | exploits/windows_x86/local/39446.py
--------------------------------------------------------------------------------------- ---------------------------------
Shellcodes: No Result
kali@kali:~$
kali@kali:~$ searchsploit -m 39446 win_x86-64/local/39525.py
Exploit: Microsoft Windows 7 (x86) - 'afd.sys' Dangling Pointer Privilege Escalation (MS14-040)
URL: https://www.exploit-db.com/exploits/39446
Path: /usr/share/exploitdb/exploits/windows_x86/local/39446.py
Codes: CVE-2014-1767, MS14-040
Verified: False
File Type: Python script text executable, ASCII text
Copied to: /Users/b/Projects/git/forks/exploitdb/39446.py
Exploit: Microsoft Windows 7 (x64) - 'afd.sys' Dangling Pointer Privilege Escalation (MS14-040)
URL: https://www.exploit-db.com/exploits/39525
Path: /usr/share/exploitdb/exploits/windows_x86-64/local/39525.py
Codes: CVE-2014-1767, MS14-040
Verified: False
File Type: Python script text executable, ASCII text
Copied to: /Users/b/Projects/git/forks/exploitdb/39525.py
kali@kali:~$You do not have to give the exact EDB-ID value (such as "39446"); SearchSploit is able to automatically extract it from a path given to it (such as "39525").
Exploit-DB Online
The Exploit Database repository is the main core of Exploit-DB,
making SearchSploit efficient and easy to use. However, some of the exploit metadata (such
as screenshots, setup files, tags, and vulnerability mappings) are not included. To access
them, you will need to check the website.
You can quickly generate the links to exploits of interest by using the -w
option:
kali@kali:~$ searchsploit WarFTP 1.65 -w
------------------------------------------------------------------------ ------------------------------------------
Exploit Title | URL
------------------------------------------------------------------------ ------------------------------------------
WarFTP 1.65 (Windows 2000 SP4) - 'USER' Remote Buffer Overflow (Perl) | https://www.exploit-db.com/exploits/3482
WarFTP 1.65 (Windows 2000 SP4) - 'USER' Remote Buffer Overflow (Python) | https://www.exploit-db.com/exploits/3474
WarFTP 1.65 - 'USER' Remote Buffer Overflow | https://www.exploit-db.com/exploits/3570
------------------------------------------------------------------------ ------------------------------------------
Shellcodes: No Result
kali@kali:~$